In May 2023, Cisco Talos published the first in-depth technical report on Intellexa’s malware called “Alien and Predator” (“Mercenary mayhem: A technical analysis of Intellexa’s PREDATOR spyware“) its inner workings and revealing the highly complex software architecture decisions required to make it work properly one such spyware on the Android operating system.
The research also sheds light on various aspects such as the commercial exploitation of surveillance software, the possibility of denial of responsibility, the effects of extensive media exposure and recruitment issues.
During LabsCon 2023 Talos (a team of world-class research analysts and engineers) presented the commercial business risks that exist using Intellexa as a benchmark.
This investigation also takes an in-depth look at Alien/Predator infections and how a “junior” malware vendor, Cytrox, was bought and turned into an Intellexa-level spyware vendor.
From the day the wiretapping scandal “broke” in Greece, enough water flowed down the drain with several journalistic research groups bringing to the public documents from a labyrinthine system that was developed offering “services” to every corner of the planet.
The “price list” of Intellexa that was leaked to the international media caused an impression, as well as the technical solutions that the company provided, as well as the fact that it managed to maintain the contamination of the devices even after restarting them.
The “progress” in the second leg was significant considering that in 2021 the Predator was impossible to “survive” the reboot of a device (Android system).
The start of development
Cytrox was first created in North Macedonia in 2017 and was then building Android-based malware. In 2018, Cytrox was acquired by WiSpear, and then in 2019, Nexa Technologies, WiSpear (and Cytrox), and Senpai Technologies teamed up to create Intellexa.
Senpai Technologies is an OSINT company based in Israel, while WiSpear, also based in Israel, specializes in Wi-Fi eavesdropping. Nexa Technologies (now called RB 42) is a company based in France with a primary focus on remote surveillance and security services.
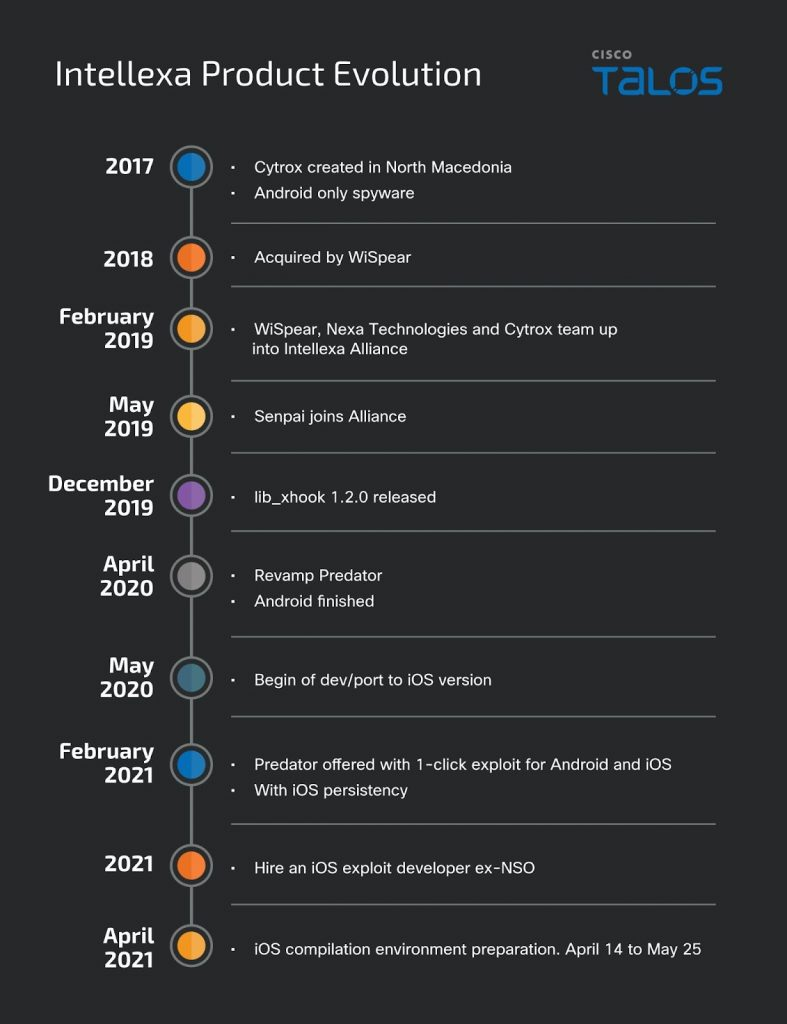
Immediately after the consolidation of all these companies, in May 2019, the overhaul of the Predator, which at that time was the flagship of interceptions for the Android operating system, began.
In April 2020, the overhaul was complete and the malware was ready to deploy (on Android). In May 2020, developers also started working on a “workaround” for iOS.
Building spyware for commercial purposes is not something that happens in the air, it is constantly evolving and a product of research. It involves meticulously bypassing the security checks put in place by mobile phone apps/packages and operating systems like Android and iOS which makes it a highly reliable “solution” and makes it particularly expensive.
That’s a lot of money
As early as 2016, the New York Times reported that NSO Group was charging $650,000 for every 10 “contaminations” and an additional $500,000 for the initial installation. The multi-year deals between the NSO Group and Mexico were valued at around $15 million back in 2013.
Five years later, in 2021, another NYT exposé reveals Intellexa’s “price list” for using the Predator, at a staggering €13.6 million for:
-20 simultaneous infections
-One-click initial access
-Predator C2 and access to hardware and software
-Project drawings, documentation, etc.
-12 months warranty support
Documents leaked in 2022 show that the Nova platform, a system to remotely and invisibly extract data from mobile phone devices, was priced at €8 million in 2022.
The two amounts above (13.6 million and 8 million euros) show that espionage programs – such as those of Intellexa – are neither for an ordinary citizen, nor for petty crime. These “solutions” are reserved for customers with deep pockets, and such spending can only be done by government agencies, the report says.
The pricing model also shows the evolution of the product. Based on the leaked dates of July 2022 Intellexa had already built the “survival” of the launcher into Android. Also increased support (for Android) to 18 months.
Intellexa’s commercial propositions are designed to create reasonable denial. These clauses range from infrastructure responsibilities to delivery methods. This is a key aspect of Intellexa’s business model, the aim is to avoid a bad reputation and claim they are not responsible for what their customers do with their ‘product’ – they claim they don’t even know who the victims are.
Possibility of disclaimer
Consistent with the Talos report above, Intellexa’s commercial propositions are designed with the ability to create disclaimers.
The clauses even extend from infrastructure to delivery methods.
This is a key aspect of Intellexa’s business model with the main goal being to avoid a bad reputation but also the possibility of disclaiming all responsibility under the pretense that they are not responsible for what their customers do with their “product” and that they don’t even know who are the “victims”.
According to what was leaked, the infrastructure and processing of information for the purpose of protecting personal data and privacy is the responsibility of the customer.
Denial allows Intellexa to claim it has no knowledge of how “victims” are being targeted. The clauses also protect Intellexa from liability in the event of public disclosure linking the malicious operations to the vendor.
Where are deliveries made?
Another critical point of the commercial activity has to do with the delivery of the supporting material (of Intellexa) which almost always takes place at a terminal or airport. This delivery method is known as ‘Cost Insurance and Freight’ (CIF), which is part of the shipping industry jargon. This mechanism allows Intellexa to claim that it has no knowledge of where the systems are deployed and ultimately located. We saw this exact scenario in action when, according to LighthouseReports (“Flight of the Predator“), Intellexa sold its software to the government of Sudan.
Everything seems to be planned to perfection. Even if we take into account terms of the offer such as “Installation and configuration at the premises specified by the customer…” and “Standard training program …” this does not mean that Intellexa can know where the hardware is located since everything can be done remotely or even without its staff.
Intellexa of course knows firsthand if its software is being used to conduct surveillance operations targeting phone number prefixes outside of its customers’ country of origin and possibly their jurisdiction. This knowledge is a consequence of the licensing model. Any sale is limited to a single telephone country code prefix but, for an additional fee, the customer may license the use of the software in additional countries without geographic restriction.
Human resources
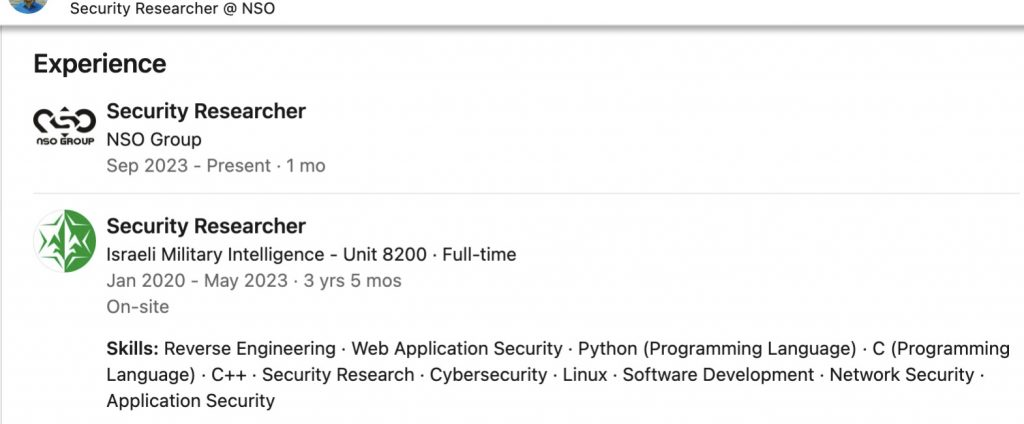
Spyware companies seem to have no problem hiring skilled manpower to develop their solutions. This is evident by looking at their LinkedIn profile. NSO Group, in June, had recruited young, highly skilled engineers from a military intelligence unit.
During the development of the iOS implant, Intellexa hired a dedicated iOS vulnerability researcher who had previously worked for the NSO Group. The timing of the hiring indicates that the company needed to integrate the implant with the exploit chain to reliably deploy it to iOS devices.
During the development of the iOS software Intellexa hired an expert who had previously worked for their group. The timing of the hire indicates that the company needed to integrate an infection “implant” with the exploit chain to deploy it on iOS devices.
Such “experts” can be found working and looking for jobs regularly at other spyware vendors as well. For example, a quick search by “Talos” showed that in September 2023 the NSO group had hired another “security researcher” with the same research background.
Target operating system support
New versions of operating systems do not seem to significantly affect Predator infections. Intellexa now supports operating system versions that go back as far as 18 months on Android and 12 months on iOS.
It should be noted that Google releases a new version per year, just like Apple. But the Android operating system may often release beta versions before the full version is made available. This gives Intellexa and exploits vendors time to develop new chains to use as initial attack vectors.
Exploitation of vulnerabilities
This is the most sensitive and least controlled part of commercial malware development. Nevertheless, one can believe that there is a sufficient impact on the functionality of a spyware vendor. But it is not exactly like that. In fact, according to the “Talos” report, the impact turns out to be low or at most moderate.
If the timeline of events is examined then one sees that it took Intellexa, at most, six months (probably less) to acquire and integrate a new fully functional chain into their software after the previous one was patched in November 2021. This is confirmed from the fact that, in May 2022, their platform is being shipped to a new customer in Sudan, according to the Lighthouse report.
In the eye of the US Department of Commerce
The methods followed attracted the attention of the US Department of Commerce, which blacklisted the well-known companies Intellexa and Cytrox.

The decision states that the Biden administration has determined that Intellexa (in Greece and Ireland) and Cytrox (in Hungary and North Macedonia) are operating against the national security and foreign policy interests of the United States.
In practice, US-based companies cannot work with the Intellexa group of companies. This means that it will have to source some of its software (exploits) from companies outside the US, which for now does not seem to be a problem. However, if the United Kingdom and the European Union take similar actions, the market will shrink, making it much more difficult for these companies to obtain the pretext to enable malware attacks.







